Computer Engineering
Innovation is key in the steadily growing computer engineering field. Our graduates are prepared for R&D, and fields, ranging from movie special effects to nanotechnology.
Electrical Engineering
Contribute to the 21st century in technological areas that you can only begin to imagine. From communications to signal processing, the department can prepare you to transform society.
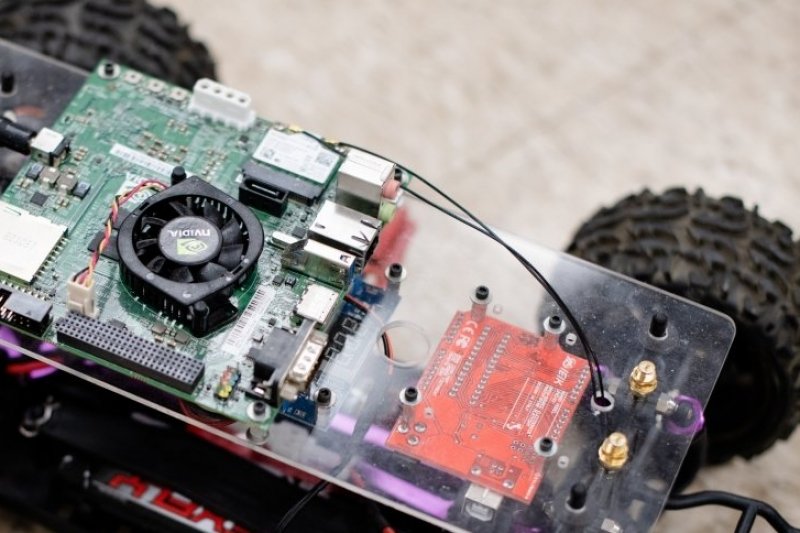
Robotics Engineering
Understand the “why” of robots and autonomous machines in a variety of settings beyond industry and manufacturing. Apply these principles to vehicles, machinery, microcontrollers, and other robotic systems.
Electrical and Computer Engineering
Students determine a flexible mix of coursework in electrical and computer engineering, engineering from related fields, physical sciences, and computer science.